YouTube Ghost Network – A malware distribution network via YouTube
Recently, security researchers at Check Point Software Technologies have issued a warning about a dangerous malware distribution network operating through the world’s largest online video-sharing platform, YouTube. Tracked under the name YouTube Ghost Network, this campaign has been active since early 2021 and has already published more than 3,000 videos on the platform. Most of these videos focus on topics such as cheats/cracks games, software piracy, or methods to bypass security protections. Through these videos, hackers distribute malicious files disguised as legitimate tools or software. To date, this campaign is estimated to have affected approximately 500,000 victims worldwide.
Details
In recent years, alongside the rapid evolution of information technology, cybercriminals have continuously adapted, refined, and evolved their tactics in order to identify more effective ways to reach users and distribute malicious software. Although email phishing remains the most common and widely used attack vector, its effectiveness has declined significantly due to the implementation of modern security measures as well as the growing cybersecurity awareness among users.
Recently, a notable shift has emerged in which attackers exploit sponsored Google advertisements or leverage Search Engine Optimization (SEO) techniques to promote fraudulent websites. By adopting this approach, combined with users’ natural tendency to trust paid advertisements or top search results, attackers can easily lure victims to malicious websites that they have carefully prepared beforehand. A clear example of this trend is the GitHub impersonation campaign used to distribute the AMOS information-stealing malware targeting macOS users, which FPT Information System Security reported at the end of September.
Cybersecurity experts from Check Point Research have recently identified a new shift in cybercriminal tactics: an invisible “network” operating on the world’s largest online video-sharing platform, YouTube. First emerging in early 2021, the network has since published more than 3,000 videos. Most of these videos focus on topics such as cheats or cracks games, pirated software, or methods to bypass operating system security protections. Tracked under the name YouTube Ghost Network, researchers from Check Point Software Technologies noted that although 2025 has not yet concluded, the number of malicious videos released through this network has already tripled compared with previous years. This rapid growth highlights the increasing effectiveness of this distribution method and presents a new challenge for maintaining overall cybersecurity in the digital environment.
The development of the YouTube Ghost Network
The YouTube Ghost Network is essentially a collection of malicious user accounts and channels operating on YouTube. These accounts exploit built-in platform features such as videos, YouTube Shorts, extended video descriptions, and community posts to promote illicit content and distribute malware by manipulating unsuspecting users.
A large portion of this network consists of compromised YouTube accounts that have been taken over by attackers. Each account is assigned specific operational roles within the channels, enabling the network to function in a coordinated and systematic manner. This structure allows the malware distribution process to operate smoothly and stealthily. When certain accounts are detected and removed by the platform, they can be quickly replaced by other compromised accounts, ensuring that the network’s overall operation continues without disruption.
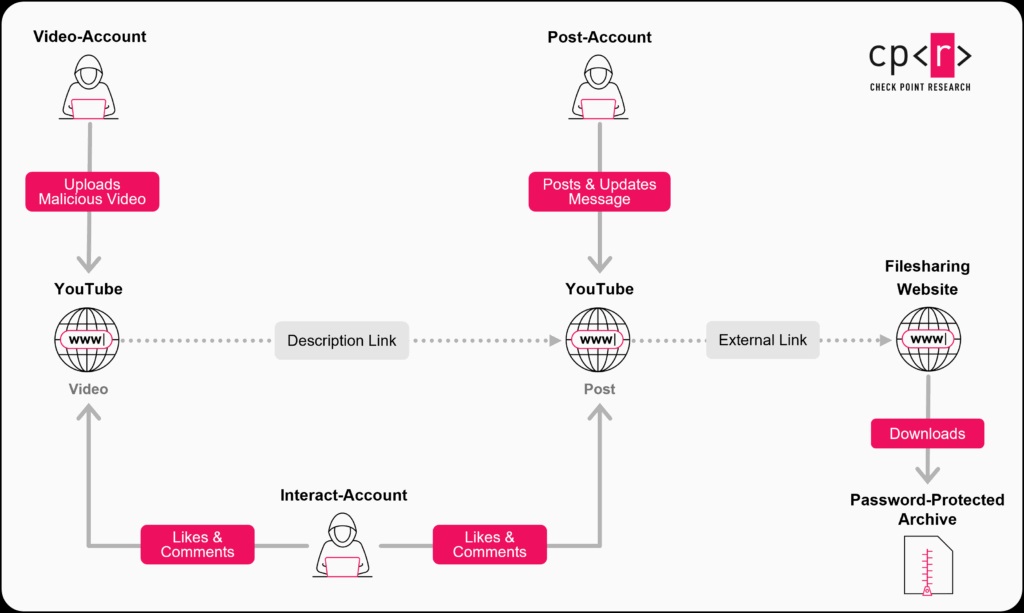
The overall structure of this network can be divided into three main roles:
- Video accounts
These accounts are responsible for uploading malicious videos and providing links to fake software packages containing malware in the video descriptions. They also include step-by-step instructions guiding users on how to download, install, and use the malicious software. To increase credibility, these accounts frequently interact with comments posted under the videos. In many cases, they pose as IT helpdesk support, responding to user questions and troubleshooting issues that arise during the installation process of the distributed malware. - Post accounts
These accounts are responsible for publishing messages and posts in the Community tab of channels on YouTube. They typically share third-party download links and provide passwords required to extract the downloaded files. A common characteristic of these accounts is that they continuously update download links and extraction passwords to evade detection. Some of them even leverage AI-powered tools to interact with comments under malicious videos, further enhancing the illusion of legitimacy. - Interact accounts
These accounts are dedicated to boosting engagement for malicious videos. Their tasks include posting comments, liking videos, and simulating normal user interactions with the content. By artificially increasing engagement, these accounts make the malicious videos appear more trustworthy and legitimate, thereby increasing the likelihood that unsuspecting users will download the malware.
During the investigation, analysts observed that the links shared by these account groups often redirect users to online file hosting and sharing services such as MediaFire, Dropbox, or Google Drive. This tactic has existed for many years and has been widely used to distribute illegal software over the internet due to its convenience and accessibility.
However, alongside this approach, researchers also discovered cases where users were redirected to malicious websites hosted on platforms such as Google Sites, Blogspot, or Telegraph. These websites are typically obfuscated using shortened URLs and contain multiple layers of malicious advertisements. In many cases, users are required to complete numerous captcha verification steps before they are finally able to download the software they were originally searching for.
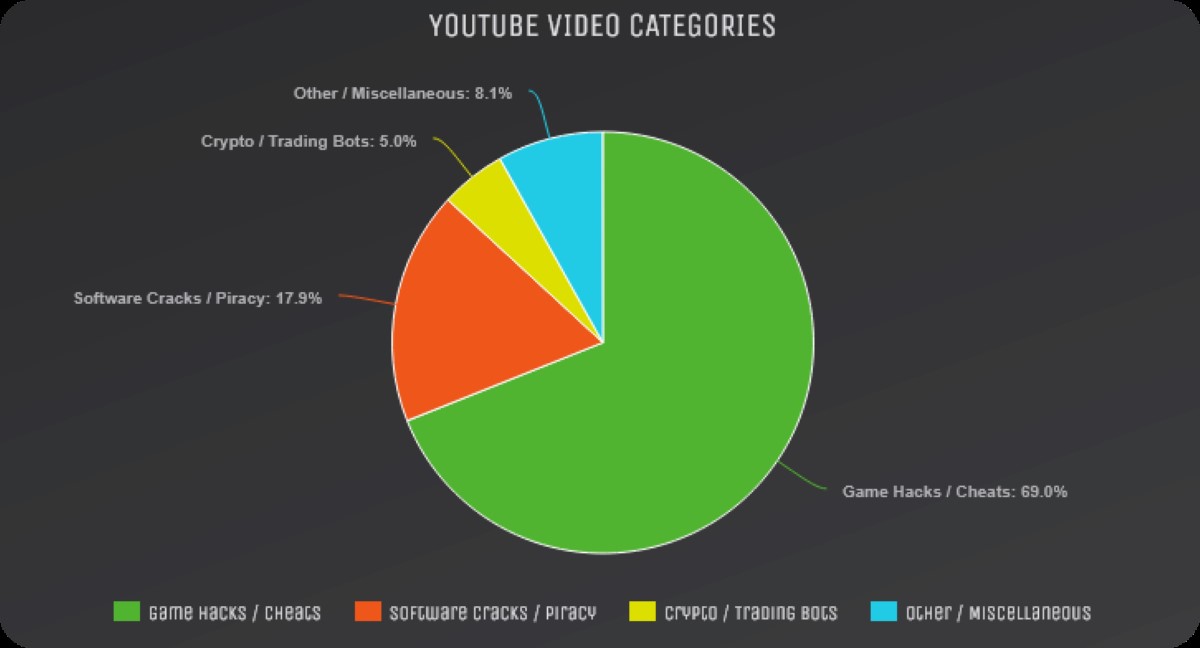
This distribution method primarily focuses on spreading well-known information-stealing malware such as Lumma, Rhadamanthys, StealC, RedLine, and 0debug. In addition, the network actively distributes NodeJS-based loaders and downloaders to diversify infection techniques, improve persistence, and better evade detection on compromised systems. According to a report from Check Point Research, the most frequently exploited theme within this network is gaming-related content. Videos containing keywords related to game hacking or cheating account for nearly 70% of all malicious videos distributed by the YouTube Ghost Network. Among them, the game most heavily targeted is Roblox.
Mitigation & recommendations
The continuous evolution of malware distribution tactics highlights the remarkable adaptability and creativity of modern cybercriminals, enabling them to bypass many traditional security defenses that are now outdated. While phishing emails remain one of the most common attack vectors, the emergence of campaigns such as the YouTube Ghost Network demonstrates how easily users can be exposed to cybersecurity risks through seemingly legitimate online platforms like YouTube.
To reduce potential risks and protect against these threats, the FPT Threat Intelligence team recommends the following best practices:
- Use official software sources
Only install and use software downloaded from the official websites of trusted vendors or publishers. Avoid downloading software from unknown websites or third-party sources on the internet. In particular, users should never use cracked software or unofficial cheating tools, as these are commonly used as carriers for malware. - Implement modern security measures
Install and regularly update reputable antivirus or endpoint security solutions. Under no circumstances should users disable security software or download tools designed to bypass or deactivate protection mechanisms. For organizations and enterprises, it is recommended to combine endpoint protection with 24/7 security monitoring solutions, which can help detect and respond to suspicious activities across the system in real time. - Enable multi-factor authentication (MFA)
All important accounts and systems should be protected using multi-factor authentication (MFA). Users should also create strong passwords, update them regularly, and ensure that operating systems and installed applications are kept up to date with the latest security patches. - Strengthen cybersecurity awareness
Human behavior remains both the most critical factor and the weakest link in many security systems. Users should actively improve their awareness of emerging cyberattack techniques and remain vigilant against social engineering tactics commonly used by attackers. Recognizing suspicious behavior early can significantly reduce the risk of falling victim to cyber threats.
Reference
- https://research.checkpoint.com/2025/youtube-ghost-network/
- https://blog.fiscybersec.com/canh-bao-phan-mem-gia-mao-tren-github-tan-cong-nguoi-dung-mac
- https://blog.fiscybersec.com/tin-tac-khai-thac-youtube-phat-tan-ma-doc-danh-cap-thong-tin
| Exclusive article by an expert from FPT IS, FPT Corporation
Mai Duc Nam Anh – FPT Information Security Center |