Atlassian Jira: Emerging security risks in the Cloud Ecosystem (Atlassian Jira: Emerging security risks in Cloud platforms)
In recent years, Software-as-a-Service (SaaS) platforms have increasingly become attractive targets for cybercriminals. A sophisticated spam campaign has recently emerged, exploiting Atlassian Jira Cloud to distribute phishing emails targeting government agencies and enterprises. This campaign leverages the inherent trust placed in widely used collaboration tools, highlighting how legitimate platform features can be abused to bypass traditional email security defenses.
Detailed findings
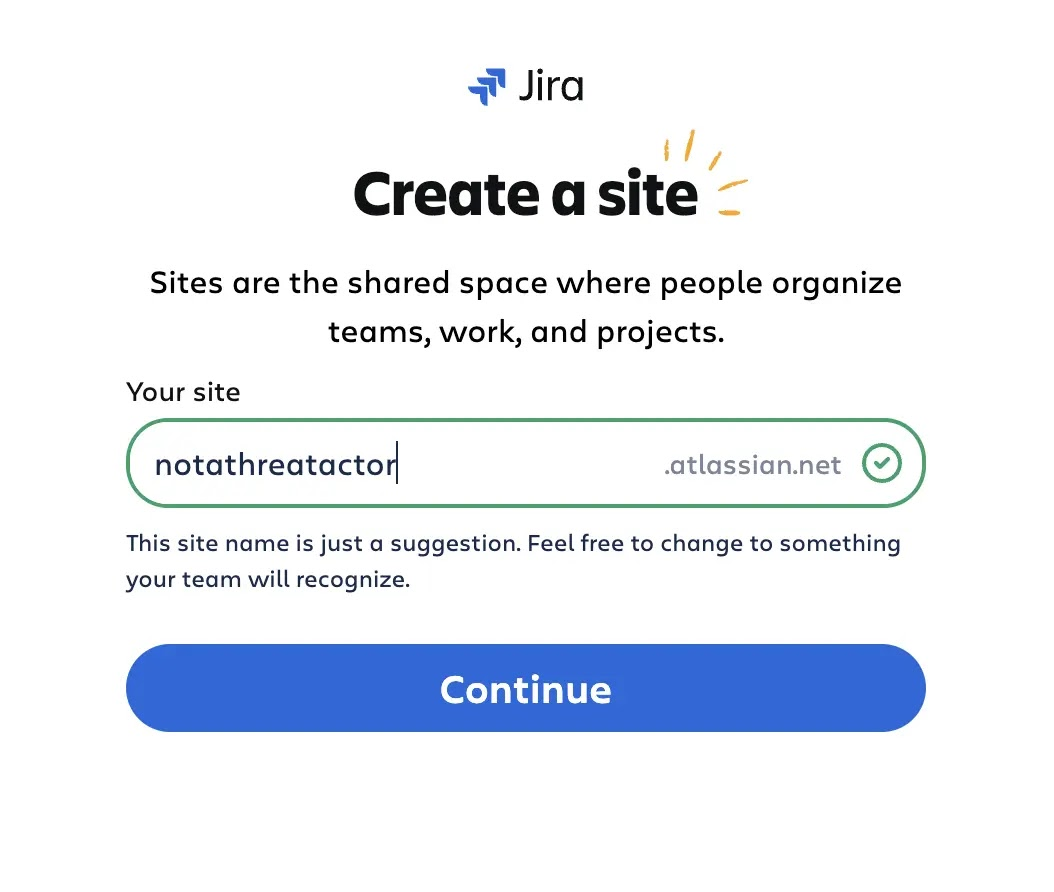
Attackers initiate the campaign by creating Atlassian Cloud accounts with randomly generated identities, enabling them to spin up multiple Jira Cloud trial instances without requiring domain ownership verification.
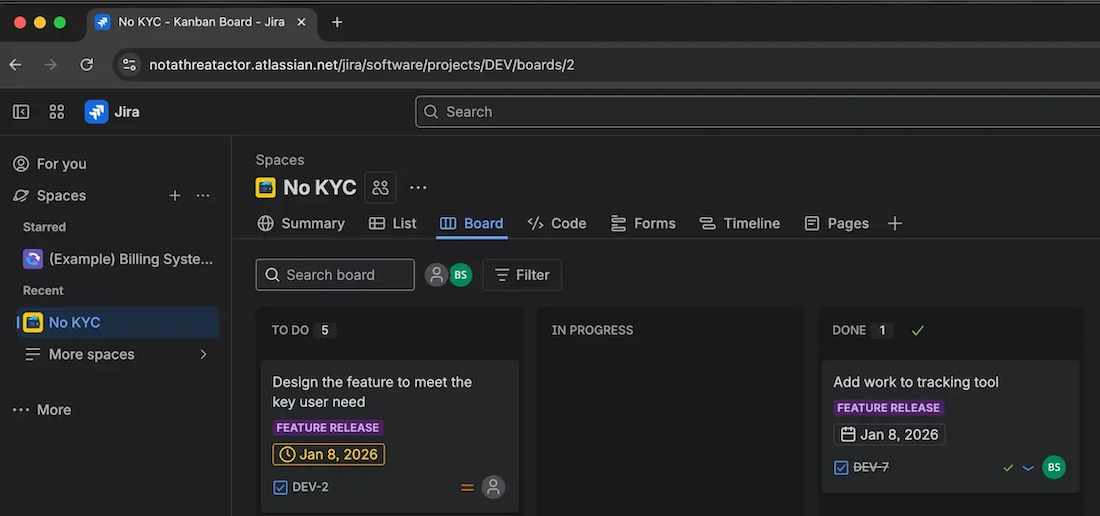
This approach allows attackers to operate with minimal traceability. Instead of relying on bulk user invitations via CSV—an action that could raise suspicion—they exploit the automation capabilities of Jira Automation capabilities (exploit the capabilities of Jira Automation) and distribute customized phishing emails.
These emails are sent from the atlassian.net domain—a highly reputable source that strictly complies with authentication standards such as SPF and DKIM—allowing them to bypass spam filters in most email systems with ease. The content is carefully localized and tailored to specific targets, such as highly skilled individuals of Russian origin living and working abroad
Victims are typically lured to phishing websites linked to fraudulent investment schemes or online casinos. In many cases, attackers leverage Keitaro TDS (Traffic Direction System) to intelligently route traffic, ensuring targets are redirected to the most convincing malicious destinations.
The campaign ran from late December 2025 through the end of January 2026, primarily targeting organizations that rely heavily on Jira and handle email communications. While financial gain appears to be the primary objective, the level of targeting suggests that additional motives may be at play.
Most email security systems rely heavily on sender-based evaluation—checking SPF, DKIM, and DNS reputation to classify spam or phishing attempts. However, this campaign exposes critical weaknesses in that approach:
- Emails are sent through Atlassian’s legitimate infrastructure → inherently trusted
- SPF and DKIM validation pass successfully → no spam alerts triggered
- Sending IPs match commonly used Jira Cloud services → not flagged by blacklists
As a result, traditional email security filters prove significantly less effective against this type of sophisticated phishing attack.
Recommendations
Based on the analysis above, FPT Threat Intelligence proposes the following measures to mitigate risks:
Monitor abnormal Jira activity
Closely track the creation of unusual automation rules or newly registered Jira Cloud instances from unverified sources. Pay special attention to emails from atlassian.net, particularly those containing suspicious links or requesting unusual actions.
Reconfigure email gateways and filtering
Establish alerts for Jira-related emails originating from outside the internal network, especially from instances that are not on trusted allowlists.
Enhance user awareness
Educate users about the risks of legitimate platforms being abused for malicious purposes. Encourage the adoption of multi-factor authentication (MFA) across all SaaS accounts.
Adopt advanced security solutions
Consider deploying advanced AI/ML-based security tools capable of detecting anomalous email patterns—even when messages successfully pass SPF and DKIM authentication.
References
Spam Campaign Abuses Atlassian Jira, Targets Government and Corporate Entities
| This article is an exclusive contribution by an expert from FPT IS, FPT Corporation.Nguyen Van Trung
|